WeTheNorth Market
Official Verification Guide
Phishing sites targeting WeTheNorth Market users are a real and persistent threat. This official verification guide teaches you how to confirm the authentic WTN onion address using PGP cryptography — the only reliable method of link verification.
Why You Must Verify the WeTheNorth Link Before Every Visit
Phishing attacks on darknet marketplace users are sophisticated, well-funded, and ongoing. Understanding the threat landscape is the first step to staying safe on WeTheNorth Market.
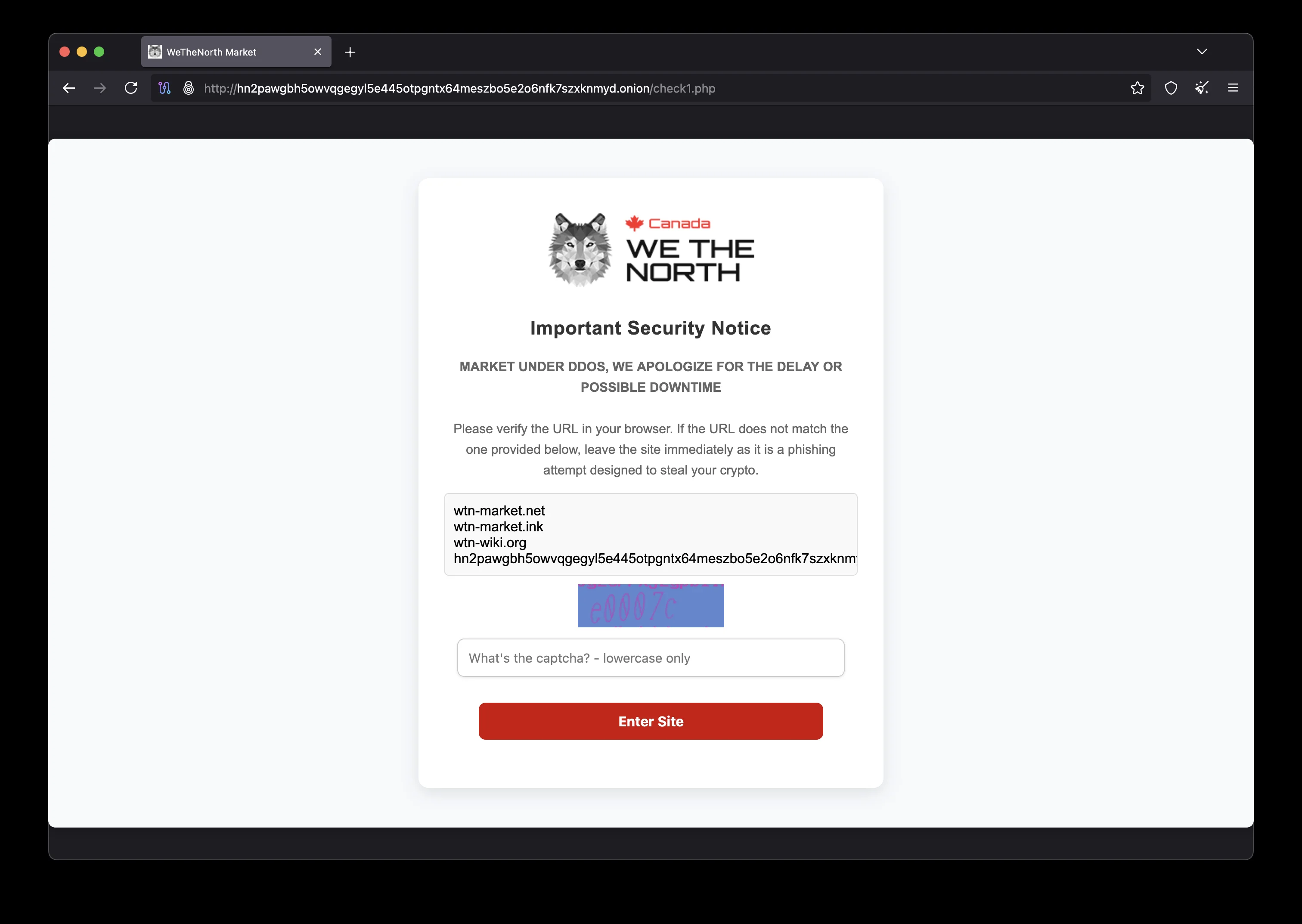
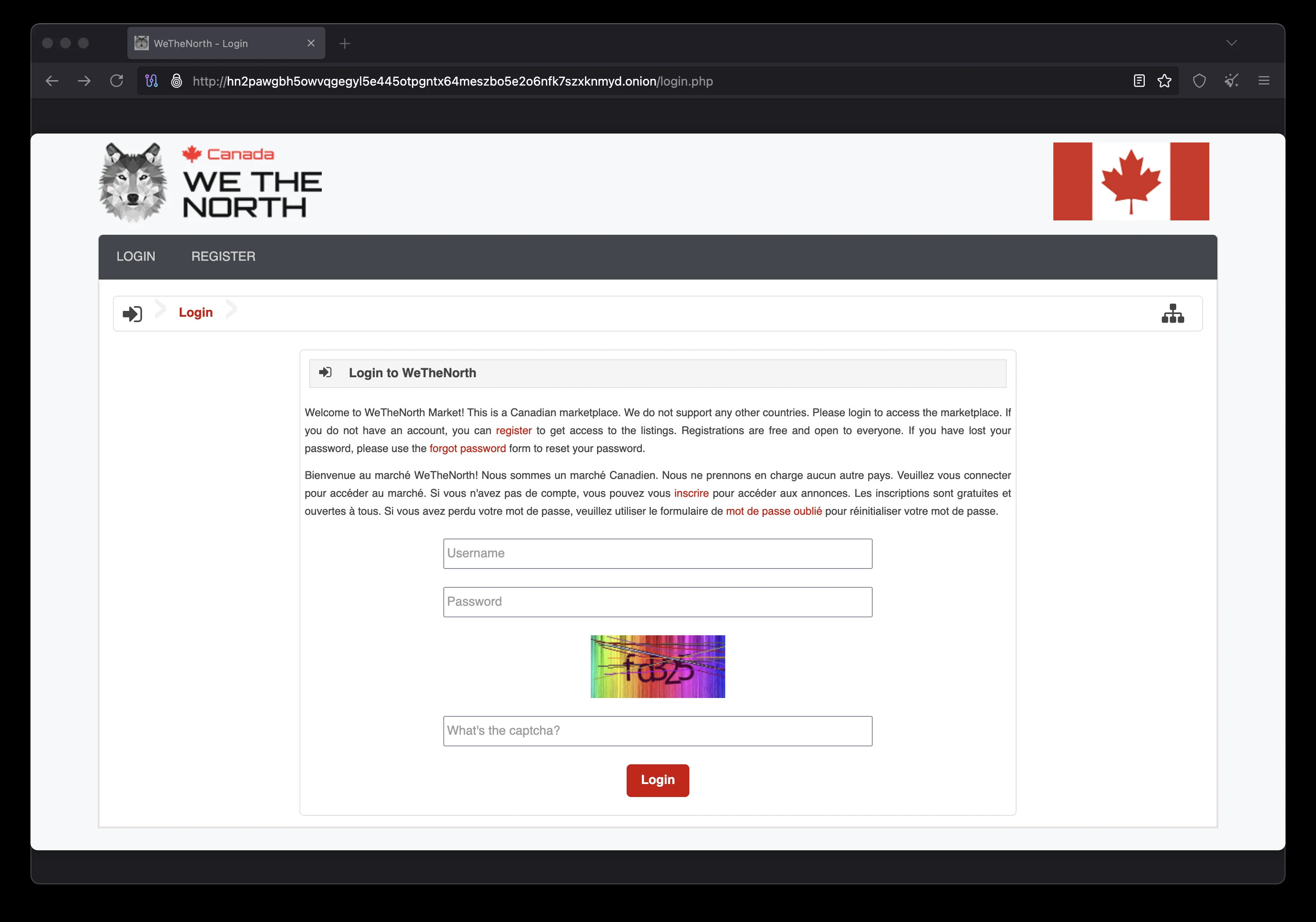
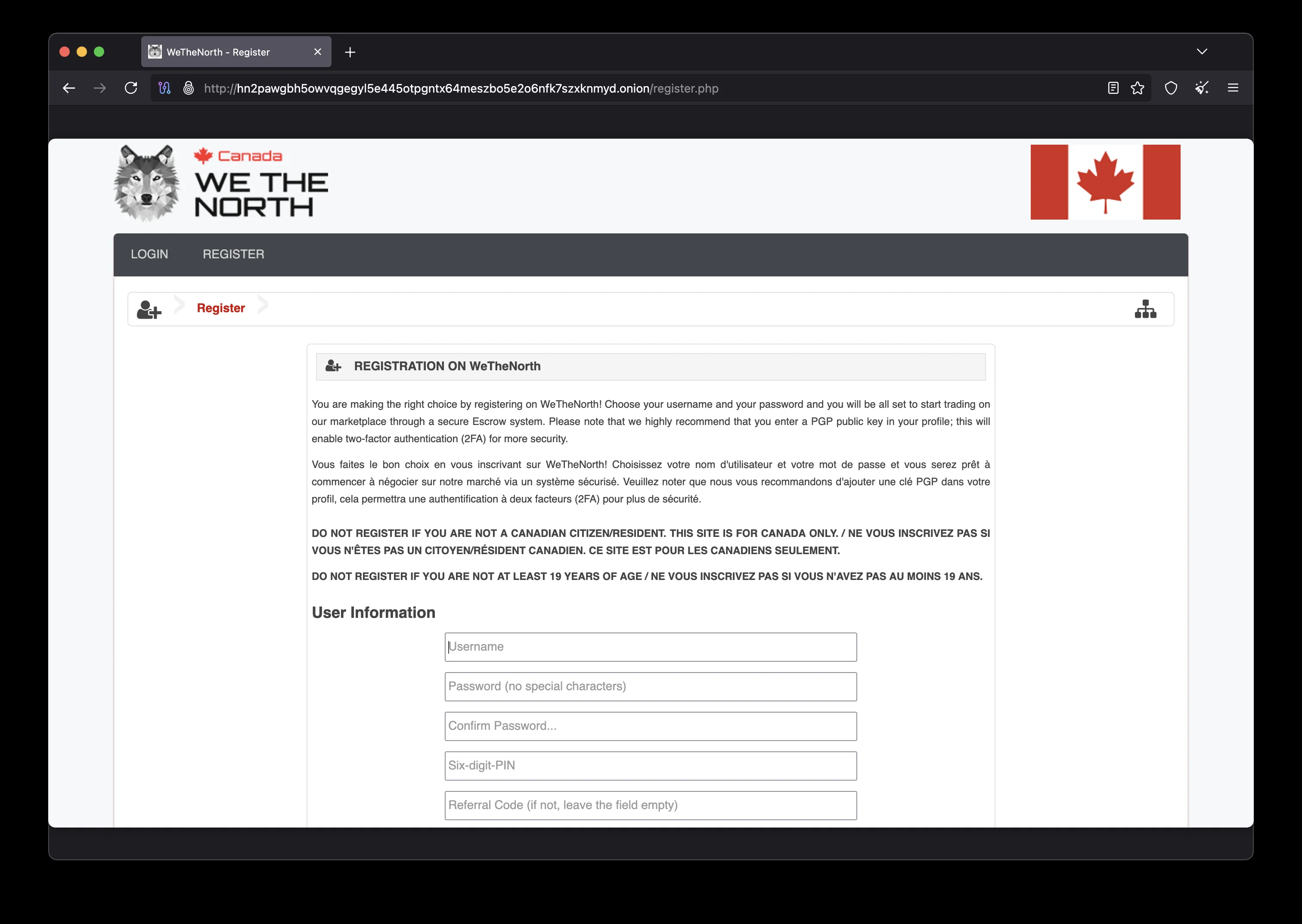
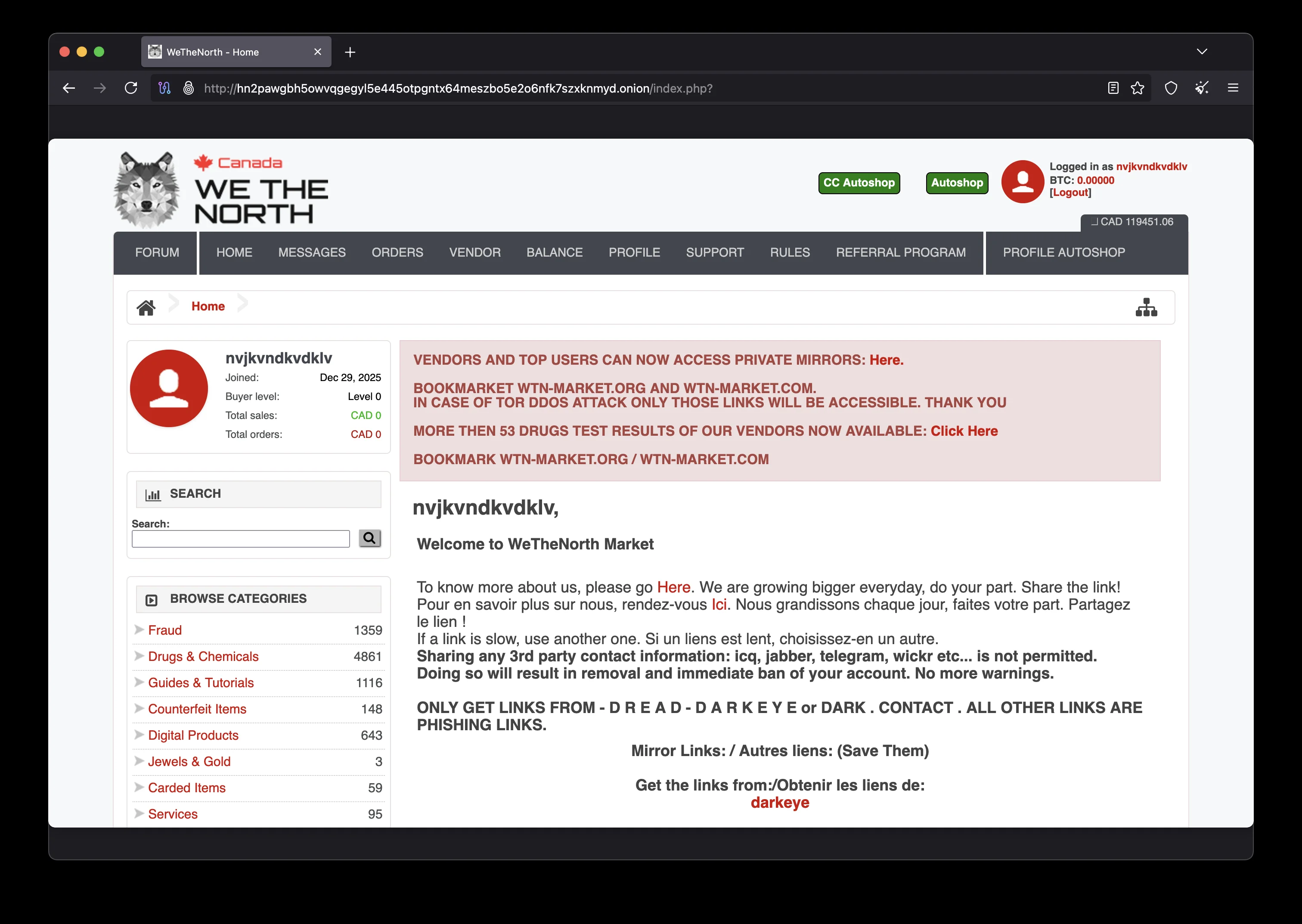
Phishing sites targeting WeTheNorth Market users have become a serious threat in 2026. These fake sites are pixel-perfect replicas of the genuine WTN interface — complete with functional login forms, fake listings, and even fabricated vendor profiles. The only difference is that when you enter your credentials on a phishing site, they are harvested by criminals who will immediately use them to drain your WTN wallet.
Phishing links spread through multiple vectors: Telegram channels claiming to share "updated WTN mirrors," Reddit posts from new accounts, Twitter/X profiles with WTN-related usernames, and even Google Ads campaigns targeting users searching for WeTheNorth Market links. These are all traps. The only safe source for WeTheNorth Market links is:
- This official subdomain: official.wethenorthdnm.world
- PGP-signed announcements from the official WeTheNorth Market signing key
- The verified mirror list at mirrors.wethenorthdnm.world
- The WTN onion access guide at onion.wethenorthdnm.world
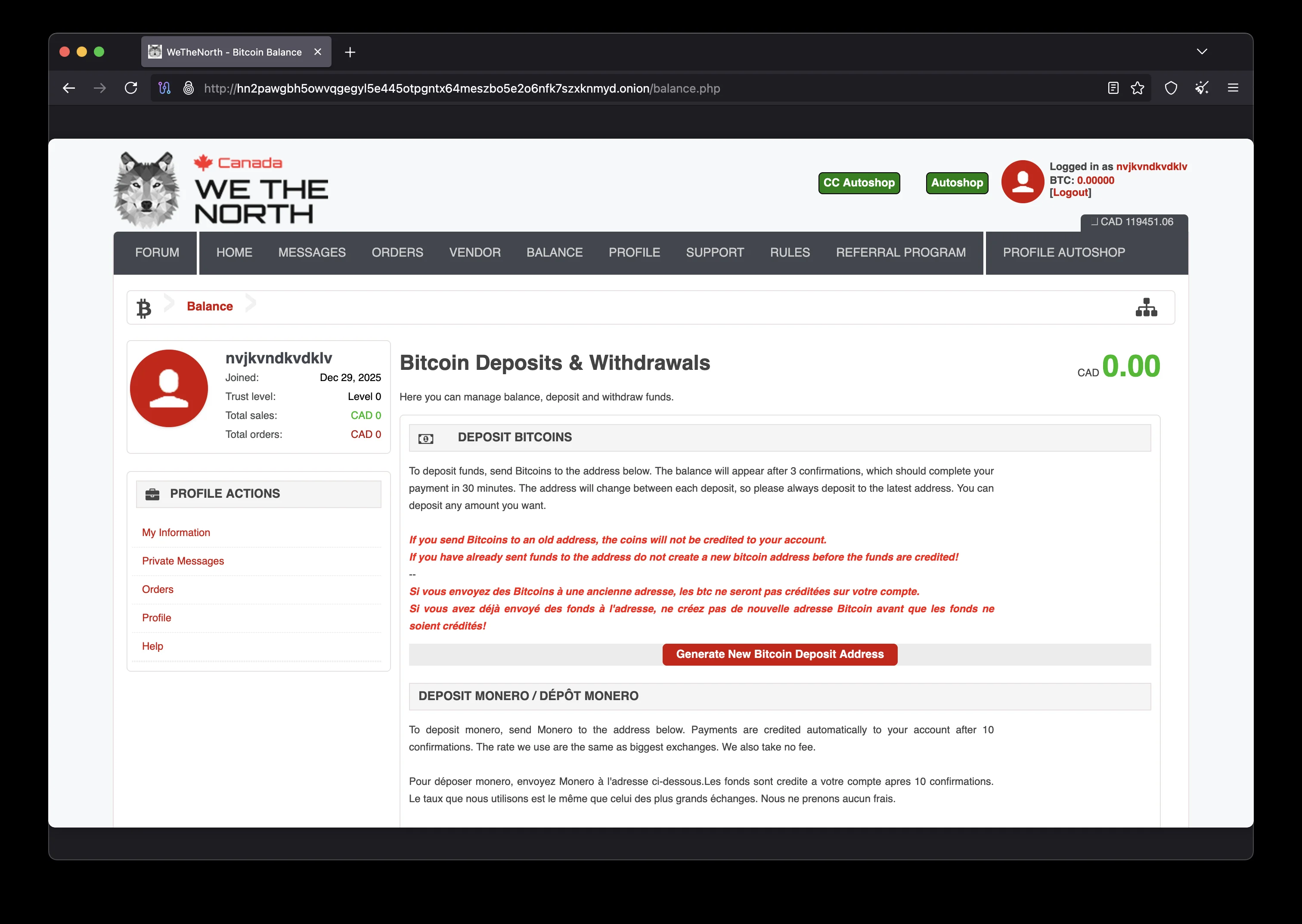
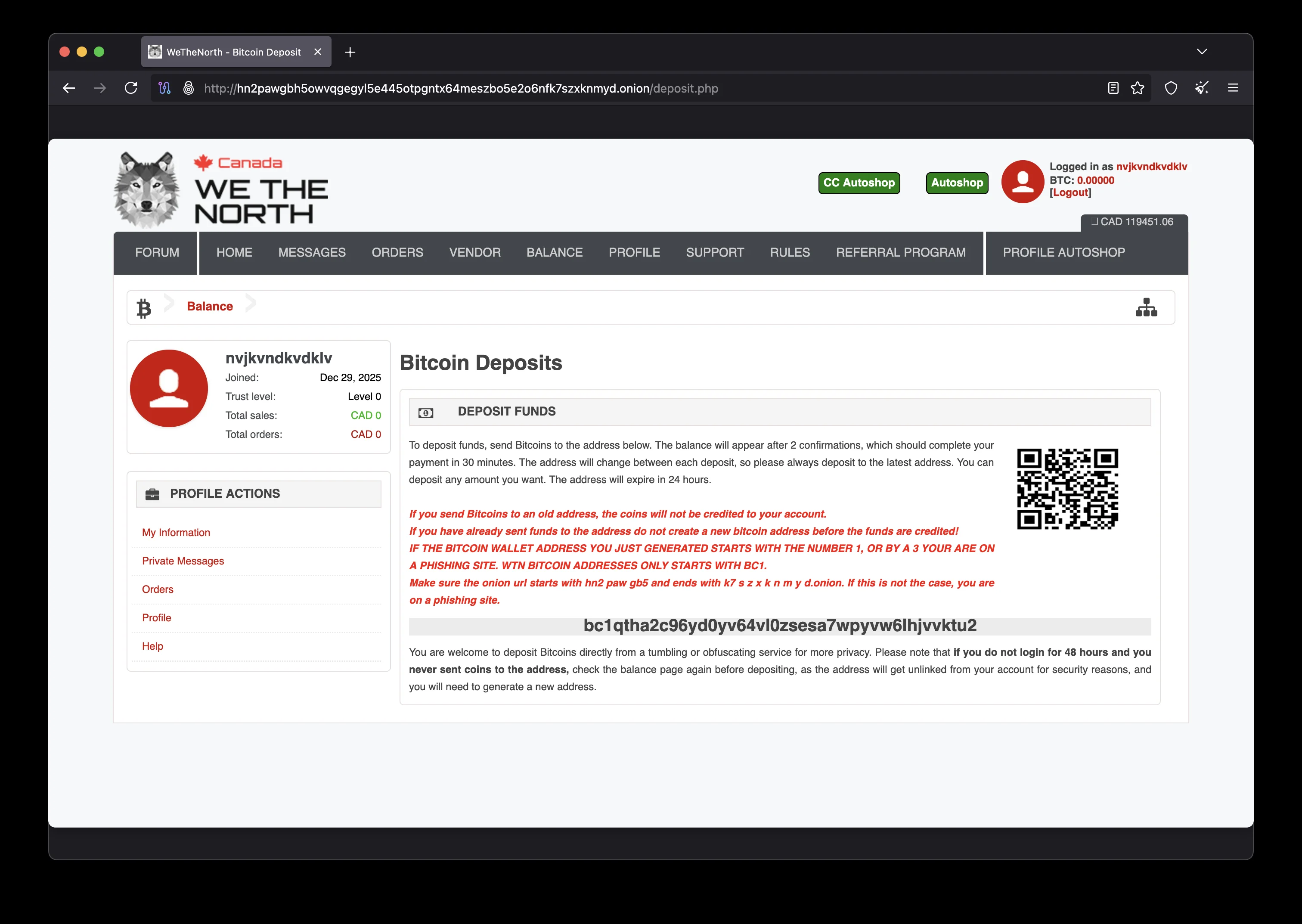
Beyond phishing for credentials, fake WeTheNorth Market sites also use a technique called "address substitution" — where the deposit address shown in your fake wallet is replaced with an attacker's address. You fund what you believe is your WTN account, but the cryptocurrency goes directly to the phisher. This has cost WTN users significant sums.
The solution is simple but must be practiced consistently: always verify the onion address cryptographically using the PGP signature on this page before every session. Then use WeTheNorth's built-in anti-phishing phrase feature to confirm you're on the real WTN site. For step-by-step PGP instructions, see our verification guide below.
The Technical Reality of Tor Onion Addresses
Understanding why phishing is so dangerous on Tor requires a basic understanding of how onion addresses work. Version 3 (V3) onion addresses — the type used by modern darknet platforms — are 56 characters long and are mathematically derived from the server's cryptographic public key. This means the address itself is proof that a server possesses the corresponding private key.
However, this cryptographic strength is only useful if you have the correct address in the first place. An attacker can generate any number of V3 onion addresses, each cryptographically valid for their own server. The challenge is not proving that an onion address is "valid" in a technical sense — all V3 addresses are valid. The challenge is proving that a specific address belongs to the legitimate platform operator and not an impersonator.
PGP signatures solve this problem. When the platform administration signs a message containing the official onion address using a PGP key whose fingerprint is widely known and verified in the community, that signature is cryptographically unforgeable. An attacker cannot create a valid PGP signature for the official WTN signing key without possessing that key's private component — which only the legitimate platform operators hold.
This is why PGP verification is the only reliable method for confirming any darknet platform link. Reputation, community posts, and other methods can all be faked or manipulated. A valid PGP signature from a well-established, community-verified key cannot. Make PGP verification a non-negotiable first step before every single session. The few minutes this takes are insignificant compared to the potential cost of a successful phishing attack.
How the Tor Network Protects Your Connection
Tor (The Onion Router) works by wrapping your internet traffic in multiple layers of encryption — like the layers of an onion — and routing it through a circuit of three volunteer-operated servers called relays. Each relay decrypts one layer to learn only the next hop in the circuit. No single relay knows both who you are and where you're going simultaneously.
The entry relay (guard) knows your IP address but not your destination. The middle relay knows neither. The exit relay — or in the case of onion services, the rendezvous point — knows the destination but not your IP. This architecture makes traffic analysis extremely difficult for ISPs, government agencies, and network observers. Combined with end-to-end encryption between your browser and the onion service, the data content of your connection is protected from all intermediate parties.
However, Tor protects network-level anonymity — it does not protect against mistakes at the application level. Logging in with a real name, reusing account credentials, or running JavaScript from untrusted sources can all deanonymize you regardless of Tor's network protections. This is why the Tor Browser security level should be set to "Safest" for sensitive activities, which disables JavaScript entirely and removes many potential attack vectors. Always keep both Tor Browser and your operating system fully updated to benefit from the latest security patches.
Verified Official WeTheNorth Onion Address
-----BEGIN PGP SIGNED MESSAGE----- Hash: SHA512 WeTheNorth Market — Official Onion Address Verification Date: 2026-02-18 Version: 2026.02 OFFICIAL WeTheNorth Market Address: hn2pawgbh5owvqgegyl5e445otpgntx64meszbo5e2o6nfk7szxknmyd.onion.onion This message confirms the above .onion address as the sole official WeTheNorth Market (WTN) marketplace link as of the date stated above. All other addresses claiming to be WeTheNorth Market are phishing sites. This subdomain (official.wethenorthdnm.world) is the only authorized clearnet presence for WeTheNorth Market link verification and official announcements. Additional verified resources: - mirrors.wethenorthdnm.world (mirror directory) - onion.wethenorthdnm.world (Tor access guide) WeTheNorth Market features: - 9,000+ listings | 300+ vendors | 4,000+ users - Operating since July 2021 - Canada-only domestic shipping - Mandatory escrow — No Finalize Early (FE) - BTC + XMR payments - 5% commission rate - Bilingual EN/FR Stay safe. Verify everything. — WeTheNorth Market Administration -----BEGIN PGP SIGNATURE----- iQIzBAEBCgAdFiEEXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXFiAACgkQXXXXXX XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX== -----END PGP SIGNATURE-----
How to Verify WeTheNorth Market Using PGP
PGP (Pretty Good Privacy) cryptographic verification is the gold standard for confirming the authenticity of WeTheNorth Market links. Follow these steps exactly.
Import the Official WTN Public Key
Import the official WeTheNorth Market PGP public key. You can retrieve it from a trusted keyserver or copy it from this page. The official WTN signing key fingerprint is published on the Dread forum by the WeTheNorth Market administration account.
gpg --keyserver keys.openpgp.org --recv-keys [WTN-KEY-ID]
Save the PGP Signed Message
Copy the complete PGP signed message from the block above — include everything from
-----BEGIN PGP SIGNED MESSAGE----- to -----END PGP SIGNATURE-----.
Save it to a plain text file (e.g., wtn-verify.txt).
Run the PGP Verification
Open a terminal and run gpg --verify on the saved file. A valid signature will show "Good signature from WeTheNorth Market" with the correct key fingerprint.
gpg --verify wtn-verify.txt
Confirm the Onion Address
After a successful verification, compare the onion address in the signed message with the one shown on this page. They must match exactly — character by character. If they match, you have cryptographically confirmed the official WeTheNorth Market address.
hn2pawgbh5owvqgegyl5e445otpgntx64meszbo5e2o6nfk7szxknmyd.onion.onion
Enable Anti-Phishing Phrase on WTN
After your first verified login to WeTheNorth Market, immediately go to Account Settings and set a personal anti-phishing phrase. This phrase will appear on every future WTN login page. If the phrase is missing or different, leave immediately — you are on a phishing site.
PGP Verification Resources
Essential tools for verifying WeTheNorth Market links:
Official WeTheNorth Sources — Where to Get Links Safely
There is a short, definitive list of sources where WeTheNorth Market links can be safely obtained. Everywhere else is potentially compromised.
This Official Subdomain
official.wethenorthdnm.world is the primary official clearnet resource for WeTheNorth Market verification. All onion addresses published here are PGP-signed and maintained by the WTN team. Bookmark this page.
WTN Mirror Directory
mirrors.wethenorthdnm.world maintains an updated list of fallback and official WeTheNorth Market mirrors. All listed addresses are verified by the WTN administration team.
Dread Forum
The Dread darknet forum hosts the
official WeTheNorth Market sub-dread (/d/WeTheNorth). PGP-signed link updates are
posted by the official WTN admin account. Always verify the PGP signature on Dread posts.
The WeTheNorth Market Anti-Phishing System
WeTheNorth Market has built multiple layers of anti-phishing protection directly into the platform. Understanding these features helps you recognize a genuine WTN session immediately.
Personal Anti-Phishing Phrase
After account creation, WeTheNorth Market allows you to set a personal anti-phishing phrase in your account settings. This unique string will appear on every WTN login page you visit. Phishing sites cannot replicate this phrase because they do not have access to WeTheNorth's database. If the phrase is absent or wrong, you are on a fake site — close Tor Browser immediately. This protection applies to both buyers and every verified seller (vendor) on the platform. Combined with multisig-style escrow, these layers make the market resistant to credential theft.
WTN Session Verification
WeTheNorth Market generates a session token on every login that appears in your account dashboard. This token changes with each session. If you notice your dashboard showing an unexpected active session from a different time, your account may have been compromised — change your password and PGP key immediately via the verified WTN link.
Always Check the Onion URL
Before entering any credentials, verify the URL in Tor Browser's address bar shows exactly
hn2pawgbh5owvqgegyl5e445otpgntx64meszbo5e2o6nfk7szxknmyd.onion.onion. There should be no additional characters, subdomains, or
variations. Phishing onion addresses are often just one or two characters different from the
real address — visually similar but cryptographically distinct.
Cross-reference this address with the PGP-signed message on this page
and with the homepage onion box every time.
Security Best Practices for WeTheNorth Users
Beyond link verification (see our PGP guide above), maintaining proper operational security ensures your WeTheNorth Market account and identity remain protected in 2026. Return to the homepage for the full feature overview.
Use Tor Browser — Mandatory
Access WeTheNorth Market exclusively through official Tor Browser. Keep it updated. Set security level to "Safest" in the shield icon for maximum protection.
Enable PGP 2FA Immediately
Configure PGP two-factor authentication in your WTN account settings within minutes of registration. A 2FA-protected account cannot be hijacked even if your password is compromised.
Store Private Keys Offline
Your PGP private key must be stored offline — on a USB drive stored in a physically secure location. Never store private keys on devices connected to the internet or in cloud storage.
Consider Tails OS for WTN
Tails OS leaves no trace of WeTheNorth Market activity on your computer. It boots from a USB drive, uses Tor by default, and wipes all data on shutdown.
Use Monero for Maximum Privacy
Fund your WeTheNorth Market wallet with Monero (XMR) rather than Bitcoin. XMR transactions are private by default — ring signatures and stealth addresses prevent blockchain tracing.
Compartmentalize Your Identity
Use a WeTheNorth Market identity completely separate from any other online presence. Never use the same username, email, or payment method across different platforms or contexts.
Use KeePassXC for Credentials
Manage your WeTheNorth Market password and security information in KeePassXC. Generate a 24+ character random password and never reuse it on any other service.
Verify Every Time, Without Exception
Make PGP verification a habit, not an occasional action. Verify the WTN link at the start of every browsing session. Phishing sites appear without warning, even on previously trusted connections.


Complete Privacy & OpSec Guide for WeTheNorth Market
Advanced operational security goes far beyond using Tor Browser. This guide covers the full privacy stack recommended for serious WeTheNorth Market users in 2026.
Understanding the Threat Model
Before accessing WeTheNorth Market, it is worth understanding who your adversaries might be and what they are capable of. At the network level, your Internet Service Provider (ISP) can see that you are connected to the Tor network, though they cannot see what sites you visit or what data you transmit. This is why using Tor Browser is non-negotiable — without it, your activity is entirely visible.
At the device level, malware, keyloggers, and screen capture tools represent a significant risk. If your device is compromised before you open Tor Browser, an attacker can see everything you do regardless of encryption. This is why security-conscious WeTheNorth Market users prefer to use a dedicated device — or better yet, Tails OS — exclusively for marketplace activity.
At the identity level, the biggest risk for most users is correlation between their marketplace identity and their real-world identity. This can happen through: reusing usernames, using the same cryptocurrency wallet for both personal and marketplace transactions, communicating about marketplace activity on platforms linked to real identity, or using delivery addresses that can be traced back to a real name.
Setting Up a Dedicated Security Environment
The gold standard for WTN access in 2026 is a dedicated, isolated computing environment. The following setup provides maximum protection:
- Boot from a Tails OS USB drive on a dedicated laptop purchased with cash
- Use Tails' built-in Tor Browser to access the market via its hidden service address
- Keep PGP private keys in Tails' encrypted Persistent Storage or on a separate encrypted USB
- Use a dedicated Monero wallet installed in Persistent Storage for WTN deposits only
- For maximum isolation, consider Whonix or Qubes OS — both offer compartmentalized security endorsed by the privacy community
- Use OnionShare to securely share files over the Tor hidden service network without exposing your identity
- Never access clearnet sites that could identify you from the same Tails session
- Shut down Tails completely after each marketplace session — it wipes all traces
Cryptocurrency Privacy Best Practices
For WeTheNorth Market deposits, the cryptocurrency hygiene principles are straightforward but critically important. If using Monero (XMR) — the recommended option — obtain XMR from a privacy-preserving exchange or through peer-to-peer trading, and transfer directly from your personal XMR wallet to your WTN wallet deposit address. Never use the same XMR deposit address twice.
If using Bitcoin (BTC), the process requires additional steps for adequate privacy. Use a coinjoin service such as Wasabi Wallet to break the transaction graph before depositing to WeTheNorth Market. Alternatively, swap BTC to XMR via a non-custodial exchange like SideShift.ai before funding your WTN wallet. Raw Bitcoin deposits from a KYC exchange carry significant traceability risk.
PGP Key Management for WeTheNorth
Your PGP keypair is the most critical security artifact in your WeTheNorth Market setup. Lose control of your private key, and an attacker can impersonate you, decrypt your messages, and compromise your account. Generate your WTN PGP keypair using GnuPG with a 4096-bit RSA key or an Ed25519 key — both are accepted on WeTheNorth Market. Use a strong, unique passphrase to protect the private key, and store the passphrase in KeePassXC.
Export your private key immediately after generation and store it offline on an encrypted drive. Back up the key in multiple secure physical locations. If you ever suspect your private key has been exposed, generate a new keypair immediately, revoke the old key using your revocation certificate, and update the public key on your WeTheNorth Market account from a verified link.
Essential Security Stack
Common OpSec Mistakes
Verification FAQ
Verified? Now Access WeTheNorth Market Safely
You've verified the official WeTheNorth link. Open Tor Browser, paste the onion address, and access Canada's most trusted darknet marketplace with confidence.
Official onion: hn2pawgbh5owvqgegyl5e445otpgntx64meszbo5e2o6nfk7szxknmyd.onion.onion
• Last updated: February 18, 2026